Network Vulnerability Testing Program
“This Network Vulnerability Testing Program is a must for cybersecurity professionals! It provides hands-on training to identify weaknesses in network infrastructure, assess risks, and implement robust security measures. By mastering techniques like port scanning, vulnerability assessment, and penetration testing, participants can effectively safeguard networks from cyber threats. A comprehensive and practical course for anyone looking to enhance their defensive and offensive security skills!”
Book your Trial Demo Class
You can call us at +91 7428748576
Network Vulnerability Testing Program Course
Network Vulnerability Testing Program
1.1 : Introduction to Computer Network
1.2 : Network Topologies and Types
1.3 : IP Addressing
1.4 : Subnet Mask, Subnetting and CIDR
1.5 : VLSM, Wild Card, Summarization
1.6 : Networking Models
1.7 : OSI Model
1.8 : Networking Device, Cabling, Network Simulator Tools
1.9 : ARP and ICMP
1.10 : Packet Flow
1.11 : Routing – Static and Dynamic
1.12 : Static Routing – Next HOP IP and Exit Interface
1.13 : Dynamic Routing - RIP, EIGRP and OSPF
1.14 : Remote Service Confriguration
1.15 : DHCP Configuration
1.16 : ACLs
1.17 : Switching
1.18 : L2 Protocols - CDP, VLN, STP, DTP, VTP
1.19 : Ether Channel
1.20 : Port Security
2.1 : Introduction to linux
2.2 : Setting Up Lab
2.3 : Exploring Kali
2.4 : Sudo Overview
2.5 : Navigating the file system
2.6 : Basic Commands
2.7 : Creating, Viewing and Editing text Files
2.8 : Managing users and Group
2.9 : Managing users and Group
2.10 : Linux Networking
2.11 : Process Management
2.12 : Services and Demos
2.13 : Log Analysis
2.14 : Archiving Files
2.15 : Debain Package Management
2.16 : Road Ahead – Towards Penetration Testing
3.1 : Introduction
3.2 : Set Up
3.3 : Variables and data types
3.4 : Numbers
3.5 : String formatting
3.6 : Booleans and Operators
3.7 : Tuples
3.8 : Lists
3.9 : Dictionaries
3.10 : Sets
3.11 : Conditionals
3.12 : Loops
3.13 : Reading and Writing
3.14 : User Input
3.15 : Exception and Error Handling
3.16 : Comprehensions
3.17 : Functions and Code Resuse
3.18 : Lambdas
3.19 : The Python Package Manner
3.20 : Python Virtual Enviornment
3.21 : Introduction to Sys
3.22 : Introduction to request
3.23 : Introduction to pwntools
3.24 : Projects
4.1 : Networking Refresher
4.2 : Linux Refresher
4.3 : Introduction to Information Security
4.4 : Introduction to Ethical Hacking
4.5 : Foot Printing / Information Gathering
4.6 : Scanning
4.7 : Enumeration
4.8 : Vulnerabilities Analysis
4.9 : System Hacking
4.10 : Malware and Threats
4.11 : Sniffing
4.12 : Social Engineering
4.13 : Denial of Service
4.14 : Session Hijacking
4.15 : IDS, IPS and Firewalls
4.16 : Hacking Web Servers
4.17 : Hacking Web Applications
4.18 : SQL Injection
4.19 : Hacking Wireless Network
4.20 : Hacking Mobile Platforms
4.21 : Introduction to IOT
4.22 : Introduction to cloud computing
4.23 : Cryptography and Steganography
5.1 : Introduction to Kali Linux
5.2 : Command Line Fun
5.3 : Bash Scripting
5.4 : Passive Footprinting
5.5 : Active Footprinting
5.6 : Advanced Scanning
5.7 : Initial access CTFs
5.8 : Introduction to Linux Privilege Escalation
5.9 : Introduction to Windows Privilege Escalation
5.10 : Root Access CTFs
5.11 : Buffer overflow overview
5.12 : Antivirus Evasion
5.13 : Active Directory Overview
5.14 : Report Generation
6.1 : Introduction to Linux Privilege Escalation
6.2 : Lab Overview
6.3 : Initial Enumeration
6.4 : Exploring Automated Tools
6.5 : Kernel Exploits
6.6 : Password and File Permissions
6.7 : Sudo
6.8 : SUID
6.9 : Capabilities
6.10 : Scheduled Tasks
6.11 : NFS Root Squashing
6.12 : Docker
6.13 : Challenge
7.1 : Introduction to window privilege escalation
7.2 : Gaining Foothold
7.3 : Initial Enumeration
7.4 : Exploring Automated tools
7.5 : Kernel Exploits
7.6 : Password and Port Forwarding
7.7 : Windows subsystem for linux
7.8 : Impersonation and Potato attacks
7.9 : Getsystem
7.10 : Runas
7.11 : Registry
7.12 : Executables Files
7.13 : Startup Applications
7.14 : DLL Hijacking
7.15 : Service Permissions (paths)
7.16 : CVE 2019 – 1388
7.17 : Challenge
8.1 : Introduction to Active Directory
8.2 : Active Directory Enumeration Principles
8.3 : External Reconnaissance
8.4 : Internal Enumerating and Footprinting
8.5 : Lateral Movement
8.6 : Enumerating and Exploiting Trusts
8.7 : Password Spraying
8.8 : LLMNR / NBT-NS Poisioning

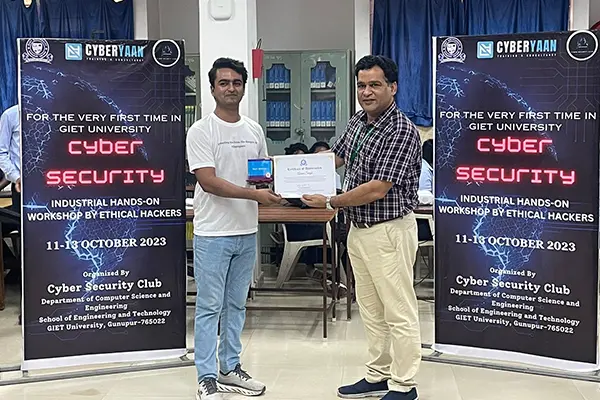
Ready to Start Your Career in Cyber Security Industry
Mobile Number : +91 7428748577 | +91 7428748576
Trending Courses
Contact Number:
+91 7428748577 | 7428748576
(175 Reviews)
(149 Reviews)
It covers a variety of topics, including network security, online application security, ethical hacking techniques, and penetration testing methodology.
Contact Number:
+91 7428748577 | 7428748576
Contact Number:
+91 7428748577 | 7428748576
(133 Reviews)
(142 Reviews)
Contact Number:
+91 7428748577 | 7428748576

Best Teaching

Convenient Practice

Video Lecture
We provide visual and auditory learning experiences, enhancing comprehension & engagement with educational content.

Live Classes