Cyber Security Training & Certification Courses
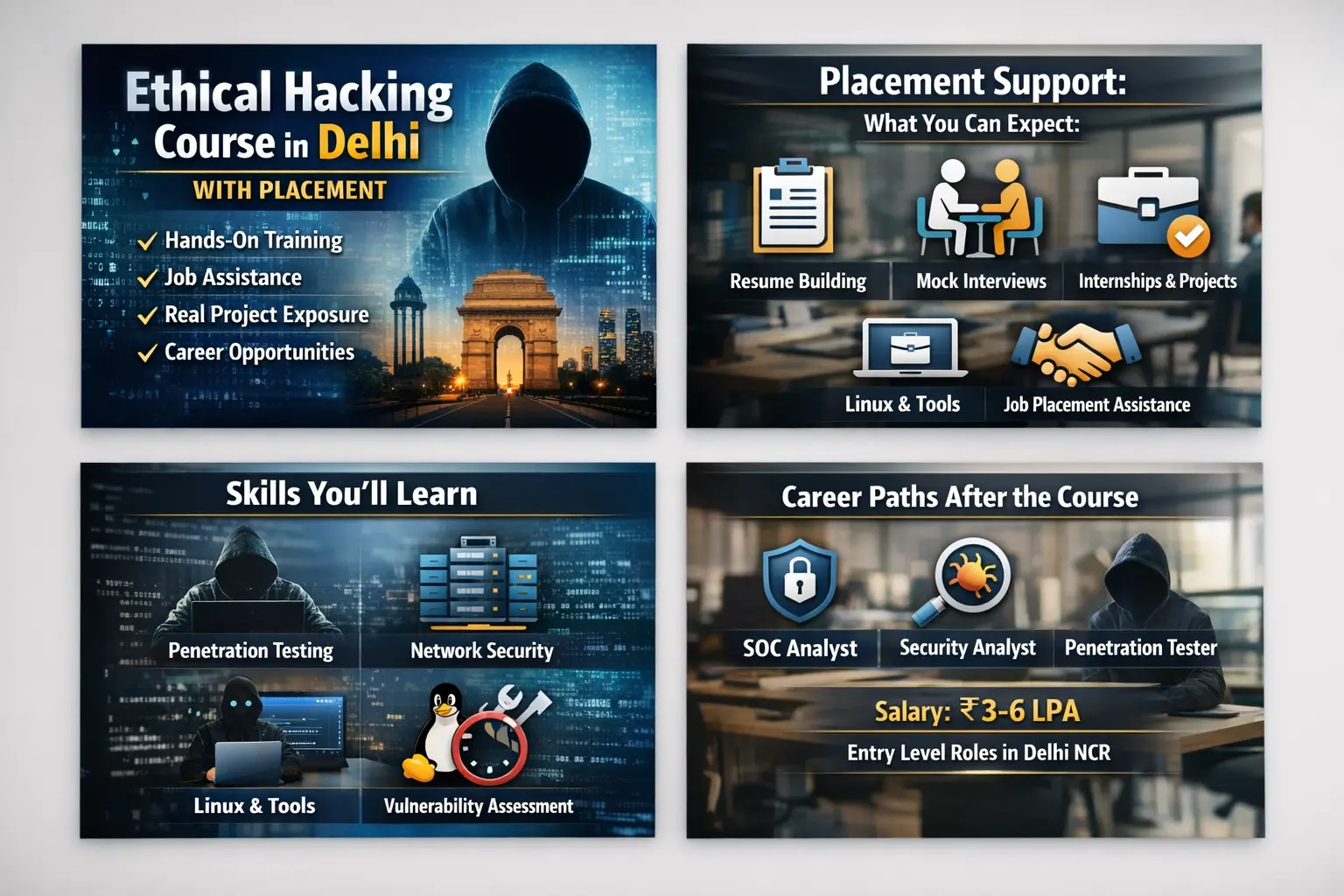
Cyberyaan Cyber Security Courses in Delhi like Ethical Hacking, Networking CCNA, Python Programming, Kali Linux.
View Course DetailsKickstart Your Cyber Security Career After 12th Class
Cyberyaan's post-12th cybersecurity program provides hands-on training, certifications and placement support.
View Course Details
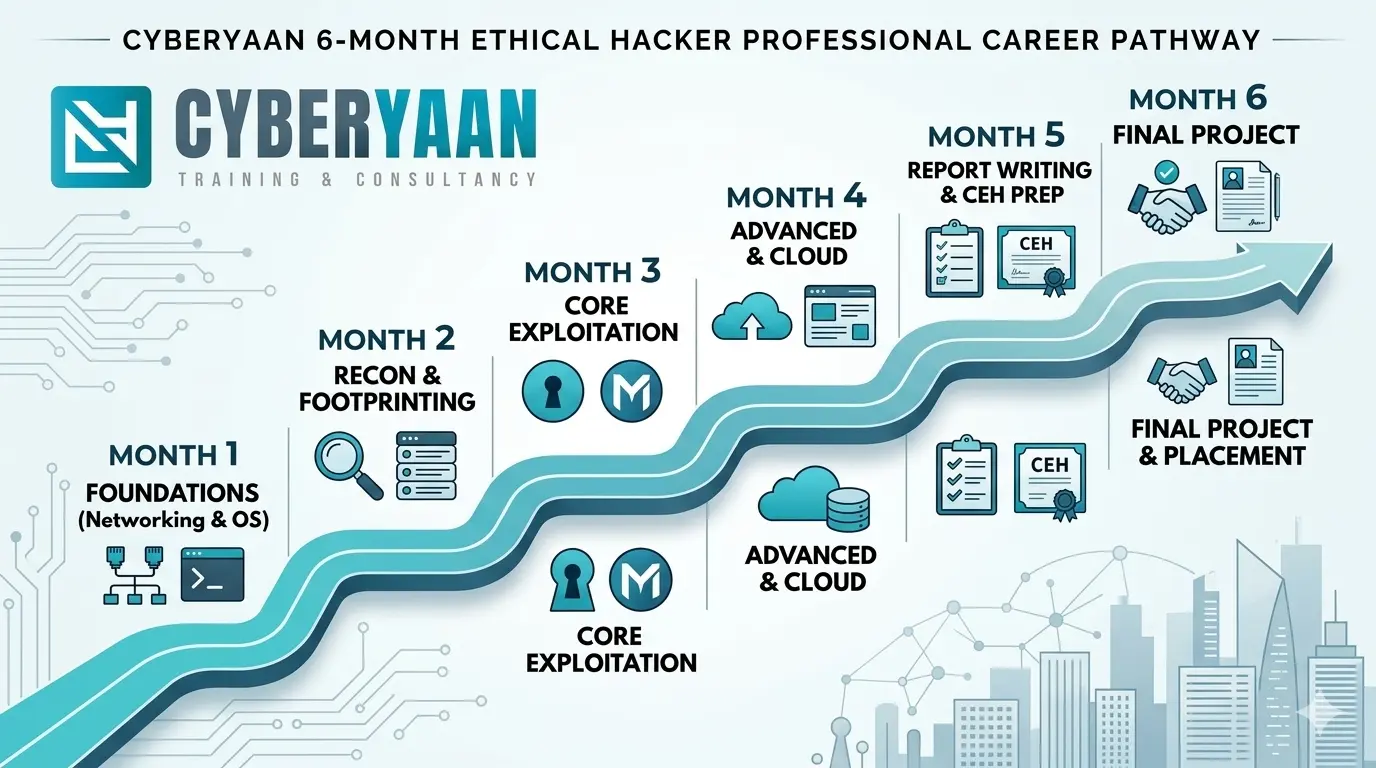
1 Year Cyber Security Diploma
Course V2
With AI
Our one-year diploma equips students with skills in ethical hacking, threat analysis and network defense.
View Course DetailsBook Your Trial Demo Class
Call at +91 7428748576
Cyber Security Diploma Course in Delhi
Cyberyaan's Cyber Security Diploma is a complete, job-oriented course that can take you from basics to career-ready in one year. With content that covers ethical hacking, penetration testing, networking, cloud security, and more, this course is the quickest way to a career in cybersecurity in Delhi NCR.
Python Programming
Write scripts, automate tasks, and build real cybersecurity tools from scratch.
Learn MoreNetwork Penetration Testing
Find and exploit vulnerabilities in Android and iOS apps before attackers do.
Learn MorePrivilege Escalation - Windows
Find and exploit vulnerabilities in Android and iOS apps before attackers do.
Learn MorePrivilege Escalation - Linux
Find and exploit vulnerabilities in Android and iOS apps before attackers do.
Learn MoreWeb Penetration Testing
Find and exploit vulnerabilities in Android and iOS apps before attackers do.
Learn MoreMobile Penetration Testing
Find and exploit vulnerabilities in Android and iOS apps before attackers do.
Learn More










Recognitions & Certifications
Cyberyaan Training & Consultancy has been recognized by leading organizations for contributing to cybersecurity training, competitions, and technical education initiatives.

BSides Pune Security Conference
BSides Pune Security Conference
DevCreate Hackathon Appreciation
DevCreate Hackathon Appreciation

NSG Manesar Training Recognition
NSG Manesar Training Recognition
0+
Students Trained0+
Certifications Issued0+
Courses Available0+
Average Rating
Kickstart Your Career:
45-Days Summer Internship Training 2026
Master any two modules from Ethical Hacking and SOC to Networking and Cloud Security with an exclusive discount. Our intensive 45-day summer program offers hands-on lab experience and expert mentorship to transform your break into a professional launchpad. Enroll now to secure your spot!
Free consultation · No prior experience required · Flexible online & offline batches
Your Next Batch Starts Soon
Whether you prefer weekdays, weekends, or fast track — a new batch is starting soon.
| # | Course Name | Start Date | Time | Duration | Mode | Action |
|---|---|---|---|---|---|---|
| 01 | Ethical Hacking & Penetration Testing | 27 Mar 2026 | 5:00 - 6:30 PM | 45 Days | Online + Offline | Book Now |
| 02 | Linux for Cybersecurity | 01 Apr 2026 | 12:00 - 2:00 PM | 30 Days | Online + Offline | Book Now |
| 03 | Networking Essentials | 01 Apr 2026 | 10:00 AM - 12:00 PM | 30 Days | Online + Offline | Book Now |
| 04 | SOC Analyst Training | 07 Apr 2026 | 5:00 - 6:30 PM | 45 Days | Online + Offline | Book Now |
| 05 | Networking Essentials | 10 Apr 2026 | 12:00 - 2:00 PM | 30 Days | Online + Offline | Book Now |
| 06 | Networking Essentials | 14 Apr 2026 | 10:00 AM - 12:00 PM | 30 Days | Online + Offline | Book Now |
| 07 | Network Penetration Testing | 20 Apr 2026 | 12:00 - 2:00 PM | 45 Days | Online + Offline | Book Now |
| 08 | Ethical Hacking / WPT | 23 Apr 2026 | 3:00 - 5:00 PM | 45 Days | Online + Offline | Book Now |
| 09 | Web Penetration Testing | 30 Apr 2026 | 10:00 AM - 12:00 PM | 45 Days | Online + Offline | Book Now |
Our Placed Students
Our students are placed in top cybersecurity companies through our training and internship programs.
Straight From Our Students
Don't take our word for it — hear directly from the students whose lives changed after joining Cyberyaan.
I had a great experience learning Python at Cyberyaan. The environment is very positive and motivating. Special thanks to Sujal Sir for his excellent teaching style and guidance. He made complex concepts easy to understand. I highly recommend Cyberyaan to anyone who wants to learn python programming in the best way!
I am currently enrolled in 1 year cyber security diploma course. Pleasant experience so far. Teachers are very helpful especially Gaurav Pathak sir and Sujal Sir. They have explained the concepts clearly and thoroughly. The teachers are highly experience and helpful and they have made the learning experience very great
"Recently Gaurav sir have teached me linux and networking in very easy pattern and I am slow learner but gaurav sir help me in all situation, gaurav sir is very supporting teacher. I recommend you to take class from gaurav sir. And cyberyaan atmosphere is very good. And teacher are very supportive and talented."
"Gaurav sir is an great trainer his teaching. style is easy to understand and explains complex concepts in a very simple way his class sessions are always informative and sir's training is very interactive i enjoy his classes grateful to have(" Gaurav sir)" as my trainer!!+â€
Cyberyaan is the best institute in Delhi for cybersecurity and ethical hacking and many more. Huge thanks to Aayush Sir for amazing teaching and to Pankaj Sir for always supporting. Everything here is top-notch -highly recommended!
"Very satisfied with the experience here, being taught by Gaurav sir currently, he is very good at explaining concepts and a great guide for me. Puts efforts in his teachings and will never fail to keep you engaged in the class."
One of the best cyber security training company. All Trainers are very knowledgeable. Highly recommend. Special thanks to my counsellor Manisha mam and My trainer Gaurav sir.
Great Support and Guidance by Tushal Sir. Cyberyaan gives best support to thier students.
In 2023 I completed training of malware analysis and now I have completed CEh v 13 and got certified Ž‰and I must say, it was a very rewarding experience. The instructors were highly knowledgeable.
I had an excellent experience with in cyberyaan . From start to finish,the service was outstanding. The team was professional, knowledgeable, and always available to answer my question.
Cyberyaan is an excellent platform for learning cybersecurity and related technologies. The training is well-structured, practical, and easy to understand, even for beginners. The mentors are knowledgeable, supportive, and always willing to clear doubts, which makes the learning experience very effective.
Excellent training institute for cybersecurity and ethical hacking. CyberYaan focuses more on skills rather than just theory, which really helps in understanding real-world security challenges. The learning environment is professional and motivating.
The Cybersecurity and Ethical Hacking training at Cyberyaan was highly informative and engaging. The trainers were knowledgeable, and the hands-on sessions provided practical experience. I feel much more confident in my skills after completing the course!"
Cyberyaan has good potential — the teaching staff is supportive and I liked the hands-on labs. However, some sessions felt rushed and a few topics weren’t covered in enough detail for real-world readiness. If you join, treat the course as a starting point — plan extra self-study or practical projects to get full value
Great experience with Cyberyaan's CEH v13 training! The course content is updated, hands-on, and very beginner-friendly. Their support team and instructors are very responsive and helpful throughout the learning journey.
I joined Cyberyaan's Ethical Hacking course recently. The instructors were very helpful, explained technical concepts clearly, and the lab‑based sessions gave real hands‑on exposure. The learning environment was supportive and doubts were cleared quickly. Overall, a good place to start if you are new to cybersecurity.
I would like to express my gratitude to Cyberyaan for their exceptional support and guidance. Their structured training, constant encouragement, and expert mentorship played a key role in my successful certification journey. Truly a reliable partner in achieving career goals. ✨
Best place for all it needs the owner is so polite and humble service is also nice very much satisfied with the work
Cyberyaan is a training institute focused on cybersecurity and ethical hacking courses with hands‑on practical instruction, industry‑aligned curriculum, and placement support
As a student at Cyberyaan, I've had a great learning experience. The trainers are supportive, the teaching is practical, and the environment is motivating. Highly recommended for anyone serious about cybersecurity
Best experience with cyberyaan, gives such useful tips to secure from basic cyber threats to school students. Special thanks to Pankaj Sir for providing this session.
CyberYaan helped me transform my interest in cybersecurity into a career path. The mentors provide personal attention, the labs are excellent, and they also keep us updated with the latest cyber news.
The best part about CyberYaan is their practical learning approach. We worked on real cybersecurity tools, SOC concepts, and even Capture the Flag challenges. This gave me an edge in my placements.
Had a really good learning experience here. The mentors are knowledgeable and explain everything clearly. Definitely recommend their courses to anyone who wants solid, practical training.
Great institute for learning CCNA concepts with practical labs, supportive trainers, clear explanations, and good guidance for networking career growth.
It was an excellent session & pure knowledge transfer. Very easy to understand & the video provided after the training is very helpful. Completely based on practical knowledge which makes it easy to understand.Thanks Sir for your support & training.
I had a great experience learning Python at Cyberyaan. The environment is very positive and motivating. Sujal Sir is an excellent teacher—very supportive and explains every concept clearly. The hands-on practice and real-world examples helped me a lot. Highly recommend Cyberyaan for anyone looking to learn coding!
Cyberyaan stands out as a leading institute for those aspiring to build a career in cybersecurity. Its blend of expert instruction, comprehensive curriculum, and practical training makes it a top choice for students in Delhi and beyond.I will highly recommend you to join Cyberyaan for betterment future
Moments That Define Us
Real Classrooms. Real Labs. Real Achievements. Take a look inside Cyberyaan.






Insights from the Cyberyaan Blog
Real insights. Real guidance. Written by cybersecurity professionals for the next generation of ethical hackers.